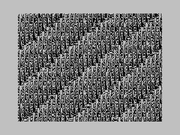
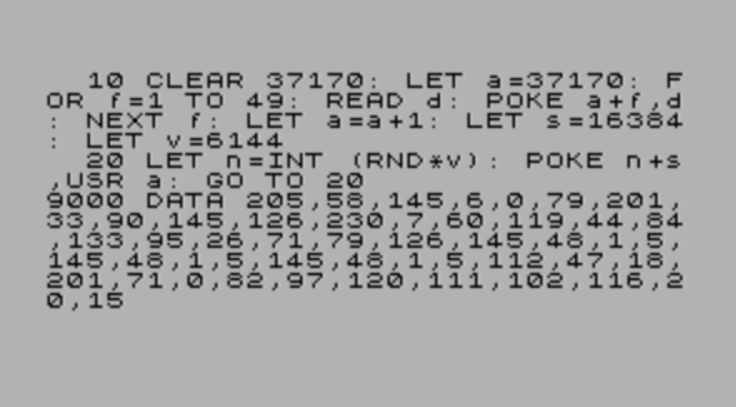
Get rid of the banding simply by doing this

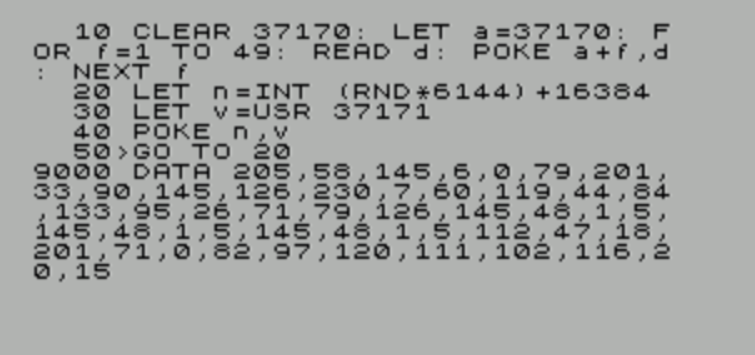
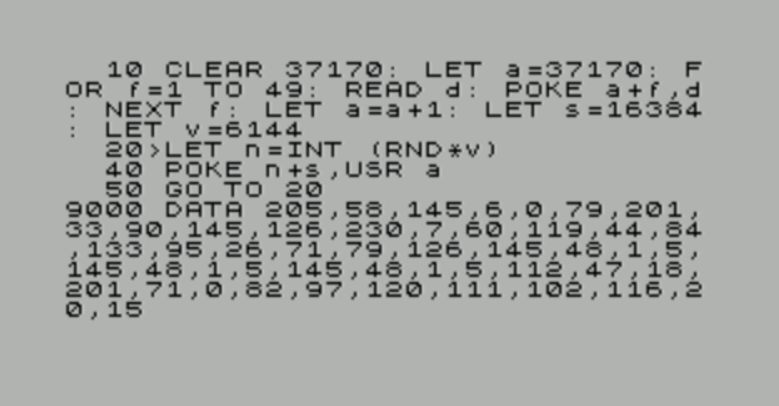
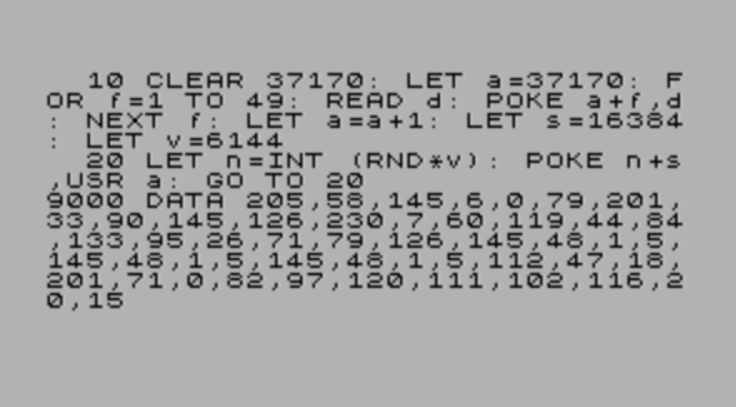
EDIT: Doing LET a = a+1 at the end of line 10 and doing LET v = USR a on line 30 probably speeds it up a bit (still slow though). EDIT2: May as well just get rid of line 30 then and do
40 POKE n,USR a
instead.
Decent RNG routine I use, thanks to Patrik Rak, Einar Sukas and Alan Albrecht.
I assembled it to where it lives in my code (address 37171) - you 'd have to assemble it manually to relocate it elsewhere. I'd already ran it a few times and messed with the seed by setting 1 byte to the R register so binary code I ripped from the debugger is going to be a little different in the table area.
Code: Select all
basic_rnd:
call rnd
ld b, 0
ld c, a
ret
; 8-bit Complementary-Multiply-With-Carry (CMWC) random number generator.
; Created by Patrik Rak in 2012, and revised in 2014/2015,
; with optimization contribution from Einar Saukas and Alan Albrecht.
; See http://www.worldofspectrum.org/forums/showthread.php?t=39632
rnd:
IF RAND_ALWAYS_1
ld a, 1
ret
ENDIF
ld hl, table
ld a, (hl) ; i = ( i & 7 ) + 1
and 7
inc a
ld (hl), a
inc l ; hl = &cy
ld d, h ; de = &q[i]
add a, l
ld e, a
ld a, (de) ; y = q[i]
ld b, a
ld c, a
ld a, (hl) ; ba = 256 * y + cy
sub c ; ba = 255 * y + cy
jr nc, $+3
dec b
sub c ; ba = 254 * y + cy
jr nc, $+3
dec b
sub c ; ba = 253 * y + cy
jr nc, $+3
dec b
ld (hl), b ; cy = ba >> 8, x = ba & 255
cpl ; x = (b-1) - x = -x - 1 = ~x + 1 - 1 = ~x
ld (de), a ; q[i] = x
ret
randSeed:
table db 0, 0, 82, 97, 120, 111, 102, 116, 20, 15
if (table/256)-((table+9)/256)
error "whole table must be within single 256 byte block"
endif
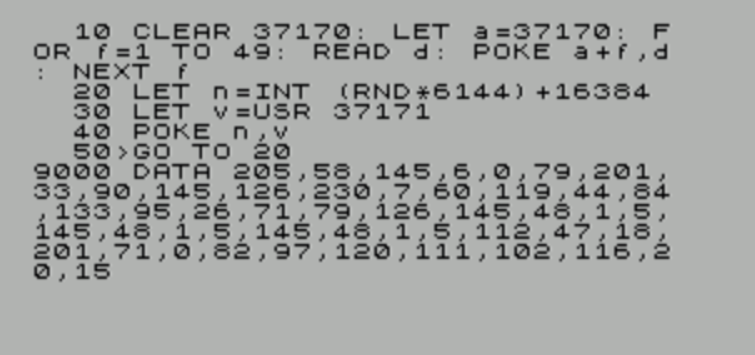
EDIT3: Final version

Obvs could be speeded up if I got rid of the RND and did the modulo 6144 stuff in ASM as well (and the pokes lol). I will leave that as an exercise for the reader.
EDIT4: Remember to paste the final version here lol

EDIT5: Final final version
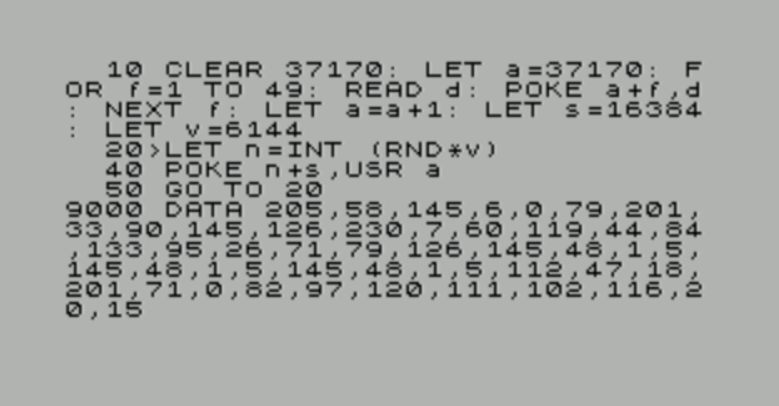
EDIT6: I lied about it being the final final version
INT is probably unnecessary as well

And ditch LET n = INT(RND*v), just do POKE RND*v+s, USR a
EDIT7: Nope that is bugged looks like INT is necessary

So POKE INT(RND*v)+s, USR a is my final answer. Does POKE really round up the first argument???